# Decrypt password with salt online
**Download links:** \
\
→ [**Decrypt password with salt online**](http://edolchozan.skyrimvr.ru/?dl\&keyword=decrypt+password+with+salt+online\&source=gitbook.com5_poster_download) \
\
→ [**Decrypt password with salt online**](http://edolchozan.darkandlight.ru/?dl\&keyword=decrypt+password+with+salt+online\&source=gitbook.com5_poster_download) \
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
\
What I do is appending a random salt bytes in front of the original bytes before encryption, and remove it after decryption. For this project, we are looking for a Google Maps API Logic Expert, that can solve for us a question about estimation price is not the same on the total amount, at the final invoice. Why did this happen? The difference between the two methods is in what the value of Y consists of.\

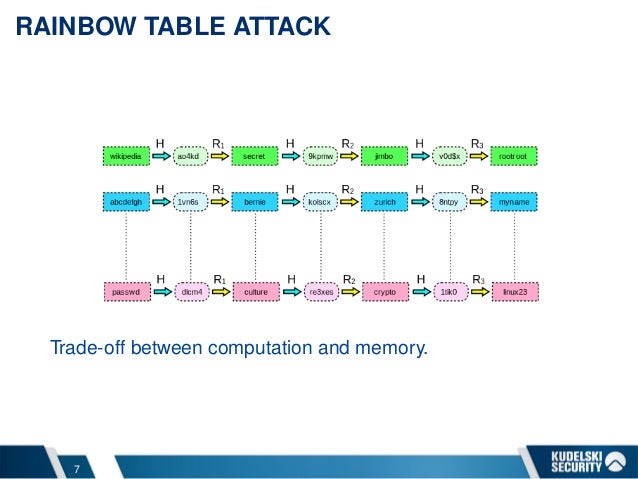
Later I want to write a notification mail to all users with powershell. Problem: SHA256 is not suitable for hash passwords because it is too fast. Core Encryption Code using System. I need to store my user's credit card hash fingerprint for future recognition, so as to always show their orders easily without going through my payment provider's card lookup. These tables are called rainbow tables. But I would think that would require more than 160 bits of randomness to be initialized e. The script works great as long as I'm looking for the user to enter a specified word into the password prompt. In the problem described, the we assume the hacker has stolen the database and can see the values of both S and Y for every user contained in the database. Problem: A salt of three characters with only letters is almost unprotected.
Main Features i want in applications. The hacker doesn't know what the password is, since it has been encrypted before storing it inside Y in the database. Now what you will do to secure your MD5 password and avoid simple cracking or hacking, let's read down.\

**how to encrypt / decrypt password with salt using libsodium php** - The weird thing is I put the variables name in my fillable property.\
I've been ask to do a task in a project that involves encryption on a windows 8. The user then provides a password and with that and the salt i should create a PKCS5 Key with 40 iterations and the key should have 32bytes length. Hopefully this will give you an idea of how to switch it over to PKCS5, but everything else I'm pretty sure is the same. It's a little lengthy, but let me know if this applies to your situation. I'm curious how much different it would be for PKCS5 instead of AES256. Core Encryption Code using System. Write bytesToBeEncrypted, 0, bytesToBeEncrypted. Write bytesToBeDecrypted, 0, bytesToBeDecrypted. ToArray ; } } return decryptedBytes; } Getting Randomized Encryption Result with Salt If we encrypt the same context i. What if we want the results different from each time it is encrypted? What I do is appending a random salt bytes in front of the original bytes before encryption, and remove it after decryption. Also I didn't copy the entire article, just the parts relevant to his question. When i've posted without quoting the parts of the article that are relevant, i'm told to quote it in case something happens to it later. You say you have done this. Step 2: Pass the supplied password and the salt from step 1 as inputs to the PKCS5 key generation method, using 40 iterations. There should be a PKCS5 class in your crypto library. The output from this step will be a key. Step 3: Use the key from step 2 and the IV from step 1 to decrypt the cyphertext from step 1. Use the specified decryption algorithm, probably AES, in the specified mode. Since an IV is supplied then it is likely that CBC mode is intended, so you will probably need to use the AES-CBC mode from your cypher library. Check the problem specification to confirm both algorithm and cypher mode -- I am only guessing here. If you have a problem with any of these steps, ask here again, showing your code and explaining the errors you are getting.
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://dating-rhonda10301992.gitbook.io/dating/decrypt-password-with-salt-online.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.